When you open a browser on your phone, what do you assume it knows about you?
Most people think: the sites you visit, maybe your location, and whatever you search for.
In reality, your mobile browser can sit at the center of a much bigger data trail. And for many Chicagoland businesses, that matters more than it sounds at first, because phones are now a normal part of work. Staff check email, open shared files, approve invoices, sign into cloud apps, and research vendors on the same device they use for everything else.
If you use Google Chrome or Microsoft Edge on mobile, you are not “doing it wrong.” They’re popular for a reason, especially in Microsoft 365 environments. The point is simply this: take five minutes to understand what your browser is allowed to access, and tighten what you do not need.
Why mobile browser privacy is easy to overlook
Mobile browsers are convenient by design. They remember logins, autofill forms, sync bookmarks, and keep you signed in. That convenience usually requires data, and some collection is normal for any browser to function.
The concern is not that your browser is automatically unsafe. The concern is how much information you may be sharing without realizing it, how long it persists, and where it can end up if an account is compromised.
Browsing data tells a story over time. It can reveal business interests, operational priorities, financial activity, employee searches, and vendor research. That is useful for advertising. It is also useful for criminals who want identifiers they can connect back to a real person and a real organization.
What to do (without changing how you work)
You do not need to toss your browser or retrain the whole team. Start with simple, practical changes that reduce exposure.
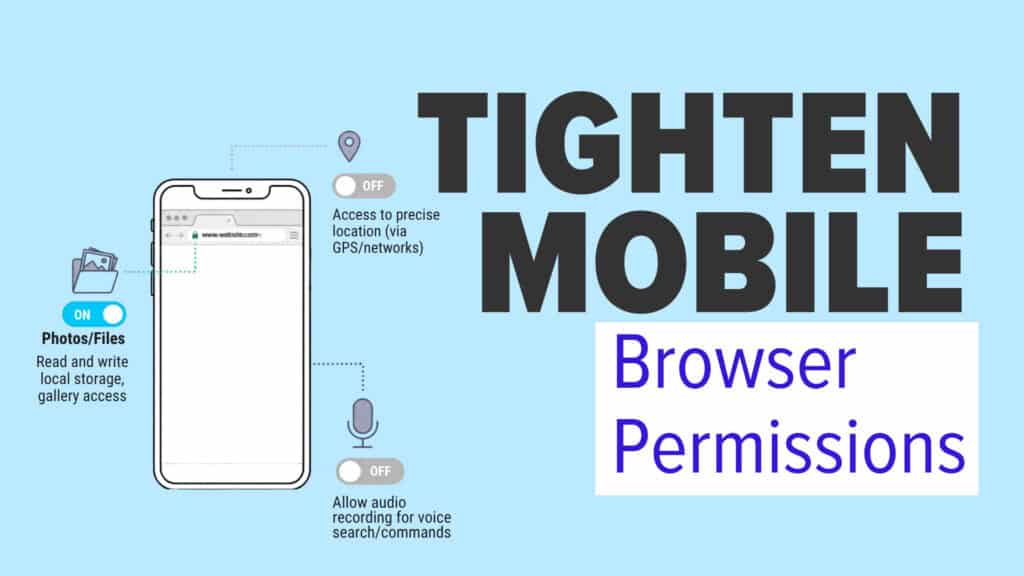
1) Check app permissions on mobile devices
On iPhone or Android, review what your browser is allowed to access.
Ask blunt questions:
- Does it need location access all the time, or only while using the app?
- Does it need access to photos, files, or media for everyday browsing?
- Does it need microphone access at all?
Most teams find at least one permission they granted casually and never revisited.
2) Tighten privacy settings inside the browser
Take a quick pass through privacy and security settings:
- Turn off unnecessary personalization and ad tracking options where possible
- Review site permissions (camera, mic, location) and remove anything you do not recognize
- Clear old browsing data on a schedule, not just when something feels “off”
Small steps, but they cut down what accumulates quietly.
3) Be intentional about sync
Sync is helpful. It is also a multiplier. If a work account is signed into a browser and sync is enabled, more data can travel across devices, and more risk can follow a compromised account.
For some roles, it may make sense to:
- Limit what syncs (passwords, history, open tabs)
- Keep work browsing in a dedicated work profile
- Separate work and personal browsing wherever possible
4) Stop relying on the browser to remember passwords
A password manager is one of the easiest upgrades you can make. It reduces the chance that credentials are sitting in places you did not intend, and it makes strong, unique passwords realistic for normal humans.
It also helps contain damage. If one account is compromised, you are less likely to have the same password reused elsewhere.
5) Use a web filtering policy that matches how your team works
A browser is a common entry point for risky clicks and sketchy downloads. A clear web filtering policy helps reduce exposure to known bad sites and categories that don’t belong on work devices. It also helps leaders answer the “are we covered?” question with something more concrete than “I think so.”
6) Sanity-check your domain and email protections
A lot of browser risk starts with impersonation, lookalike domains, and fake login pages. If you want a quick health check, our domain health diagnostic tool can help you spot issues tied to DNS and email authentication that influence trust and deliverability.
The goal is not paranoia. It’s being deliberate.
You can keep the same browser. You can keep the same workflows. You just want fewer silent leaks in the background.
For most Chicago-area organizations, mobile browser privacy is one of the most overlooked parts of cyber hygiene, mostly because it feels personal instead of operational. But phones are now part of operations, and browsers are one of the most used tools on those devices.
If you want help tightening mobile privacy, setting a workable web filtering policy, or validating your environment with Domain Health, get in touch.