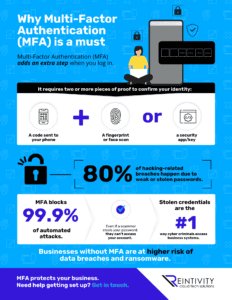
Find out how Multi-Factor Authentication has contributed to the adoption of cloud computing by numerous enterprises in recent years. Learn how multi-factor authentication functions and why businesses should aim to add more layers of authentication to their systems to make it more difficult for hackers to breach them.
How Multi-Factor Authentication played a significant part in cloud computing
by Reintivity | Aug 13, 2022 | Non-profit, Video